12 Scanners to Find Security Vulnerabilities and Misconfigurations in Kubernetes | by Walid El Sayed Aly | Towards Dev
12 Scanners to Find Security Vulnerabilities and Misconfigurations in Kubernetes | by Walid El Sayed Aly | Towards Dev
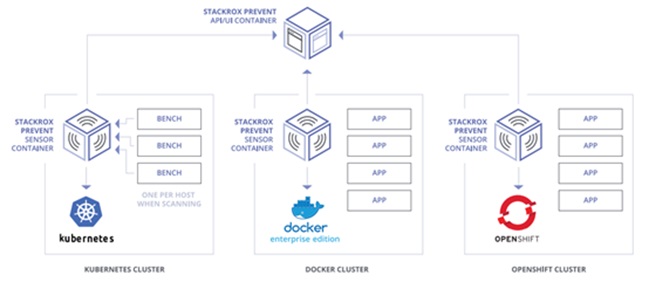
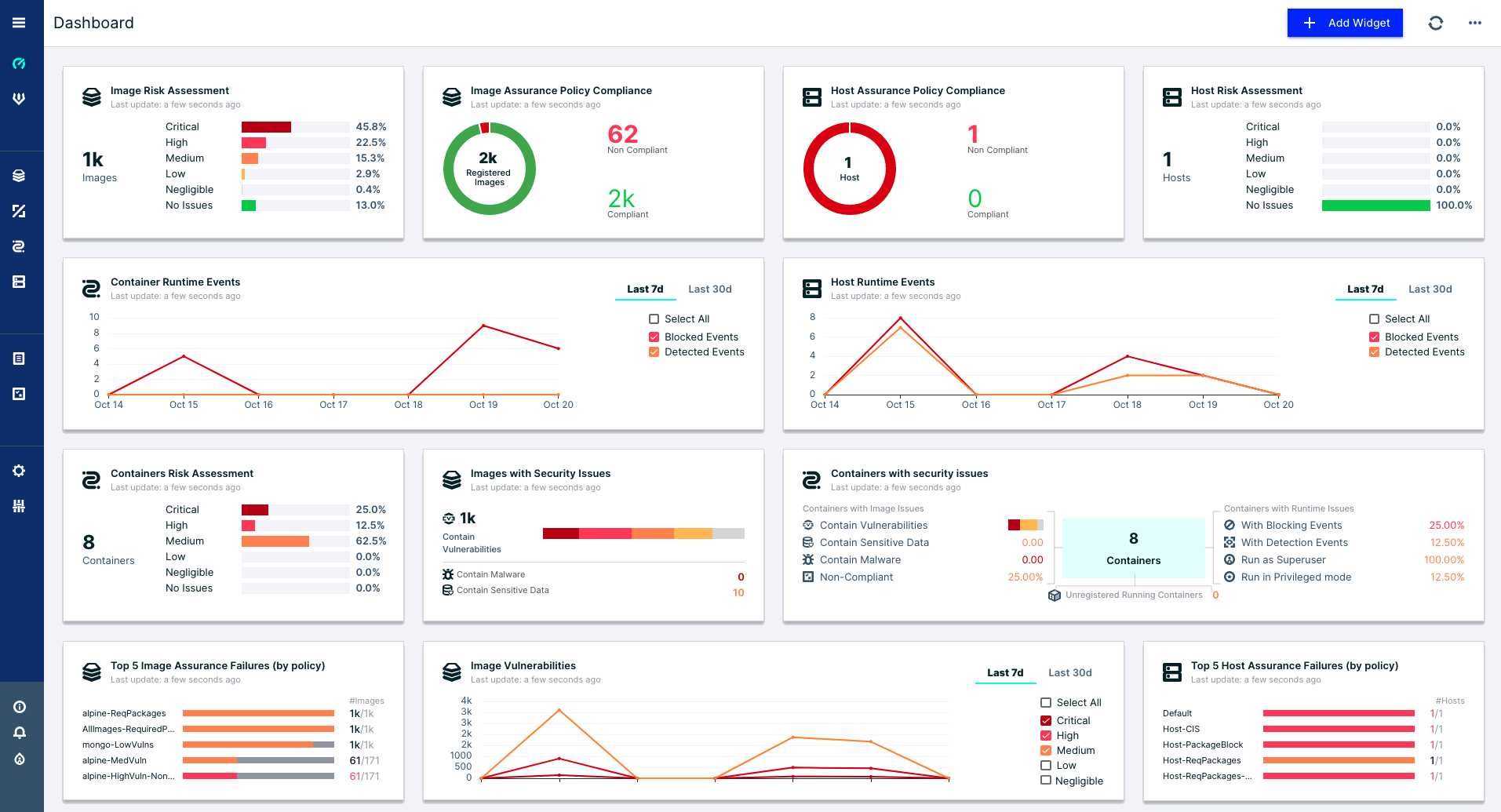
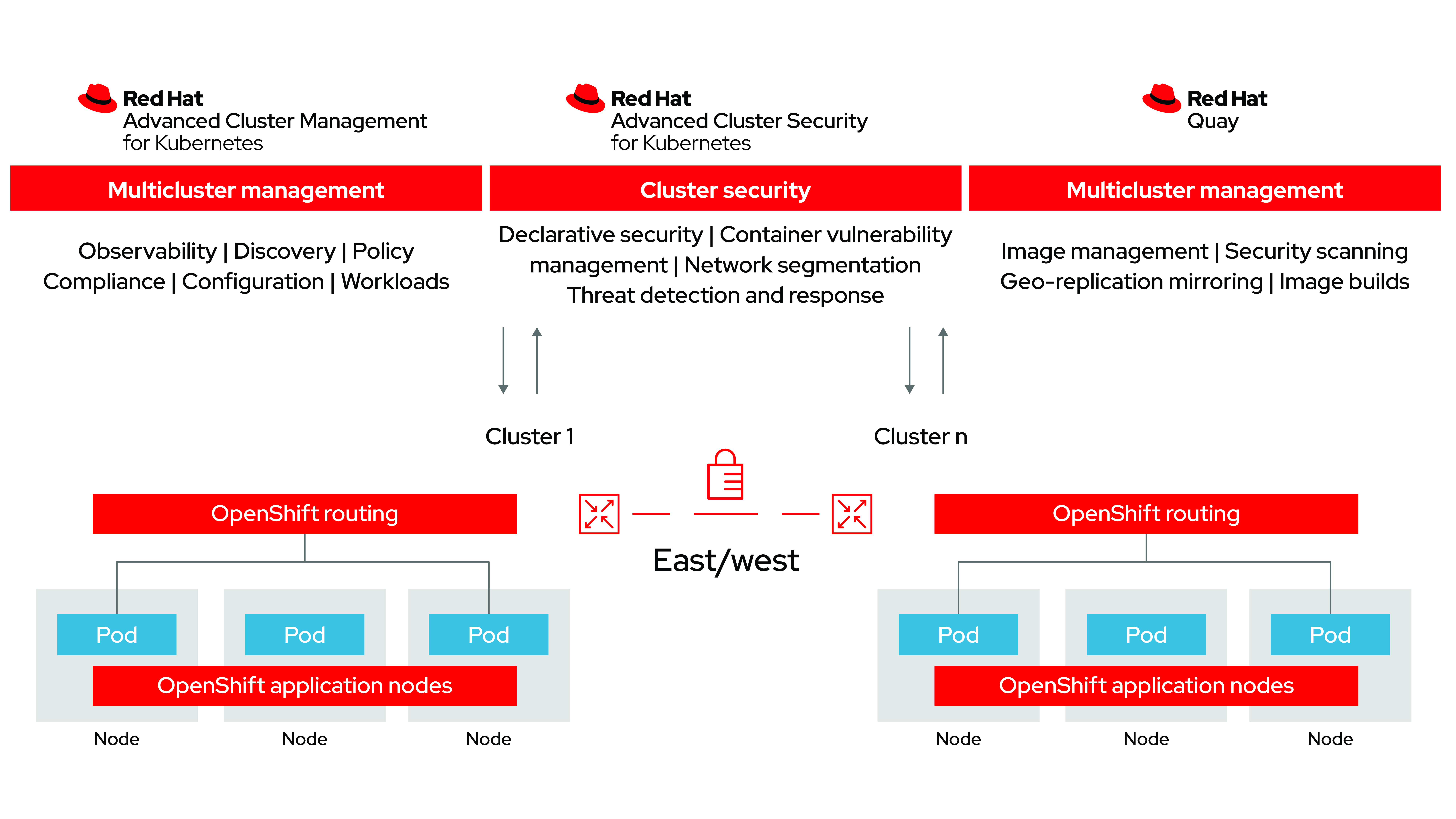
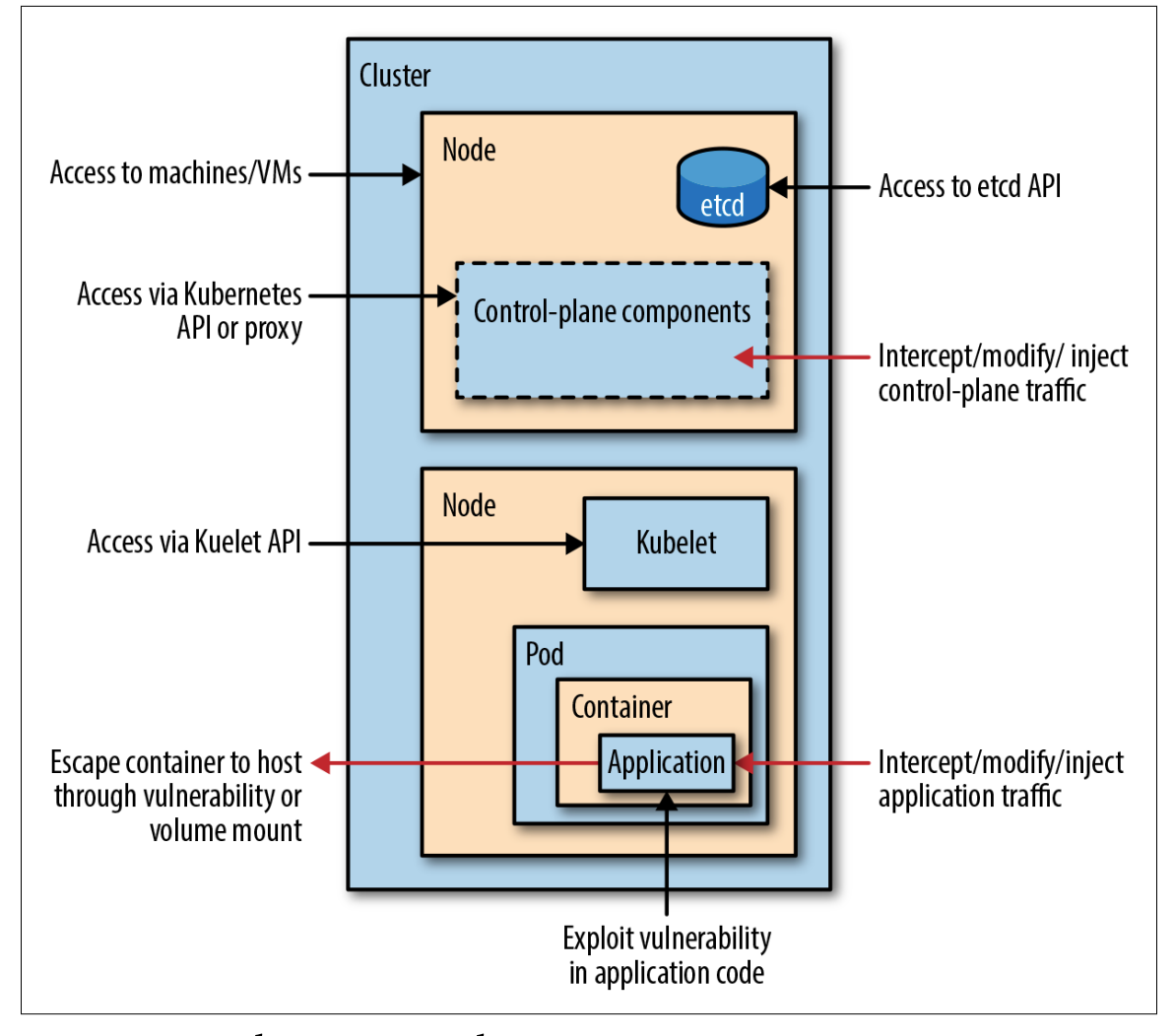
Technical Report on Container Security (V)-3 - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

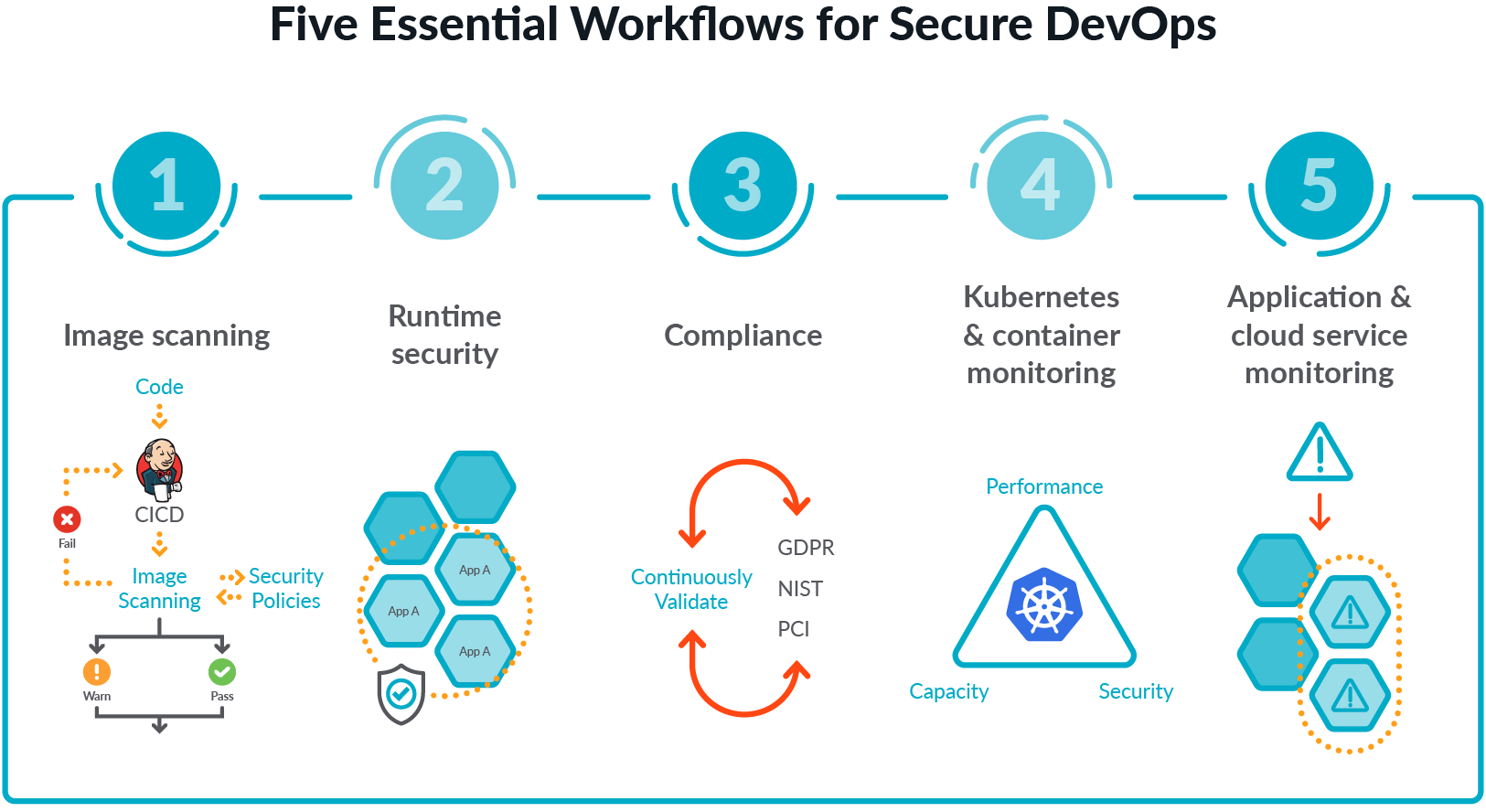
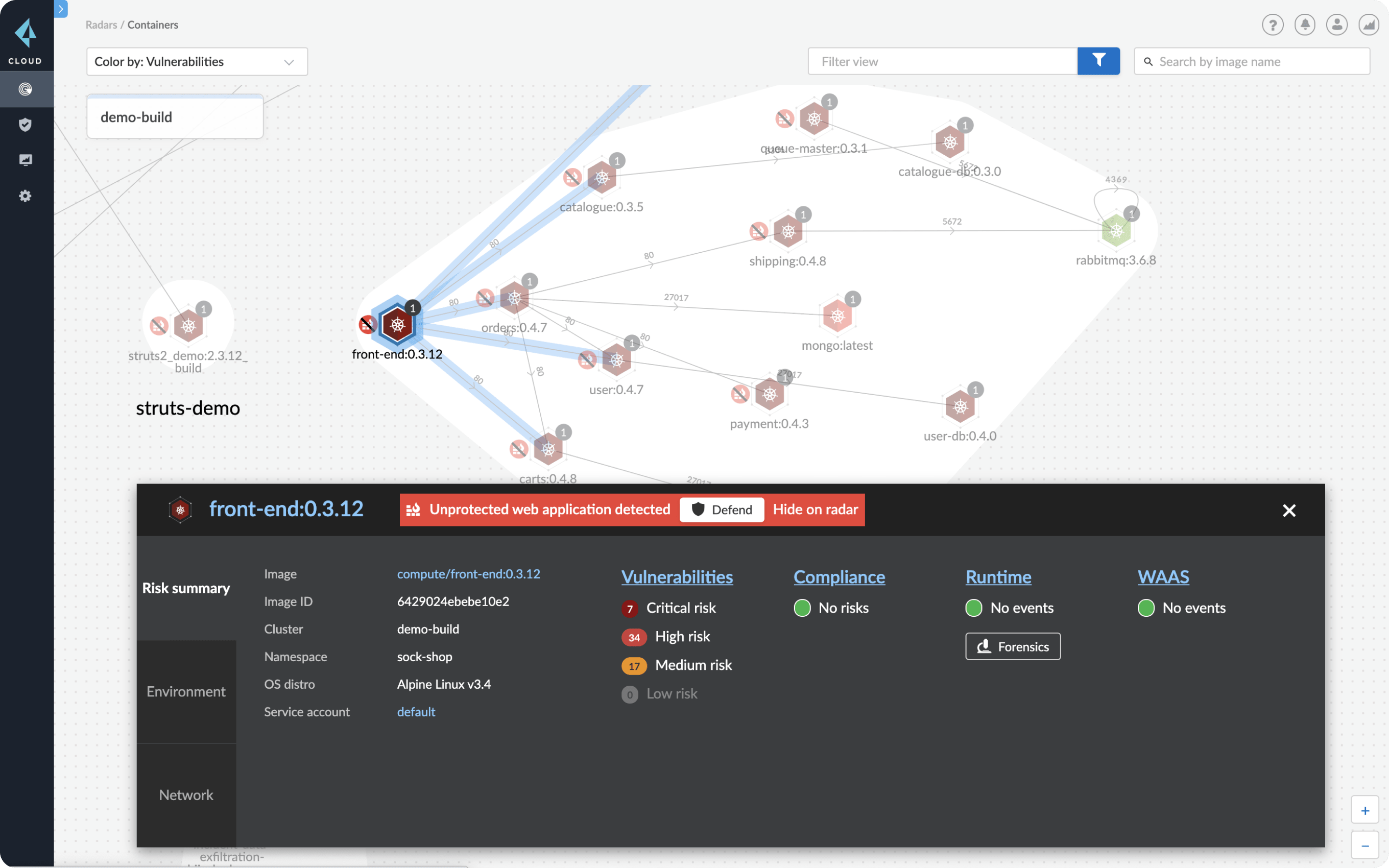
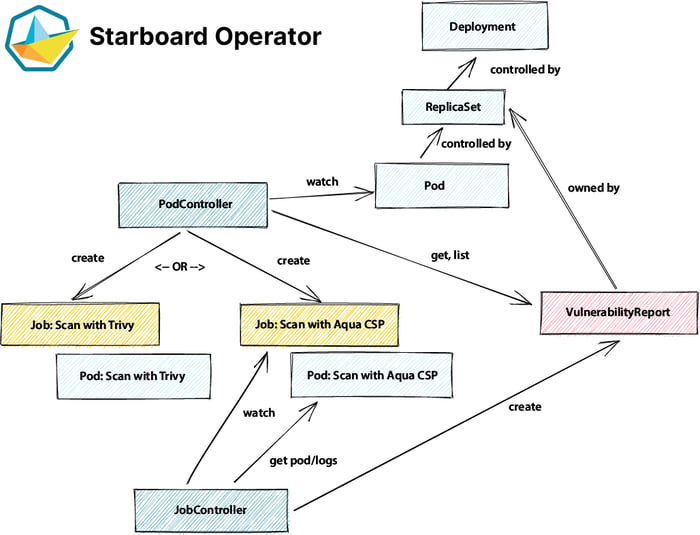
12 Scanners to Find Security Vulnerabilities and Misconfigurations in Kubernetes | by Walid El Sayed Aly | Towards Dev
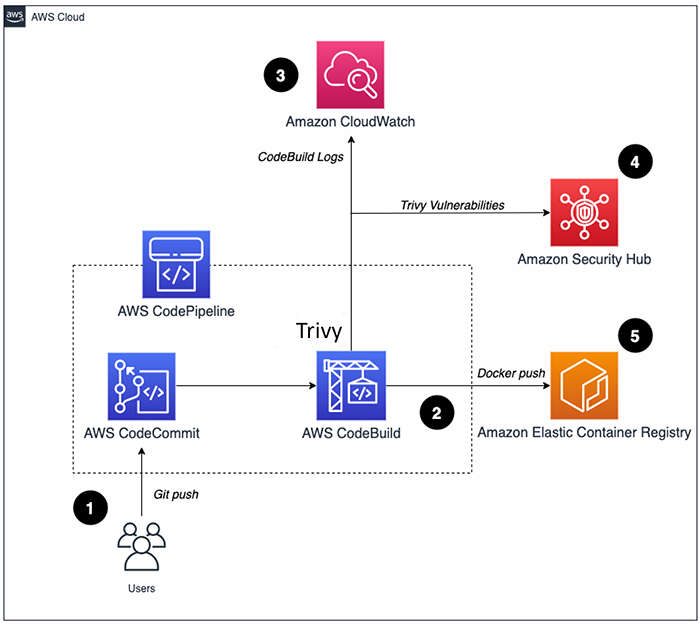
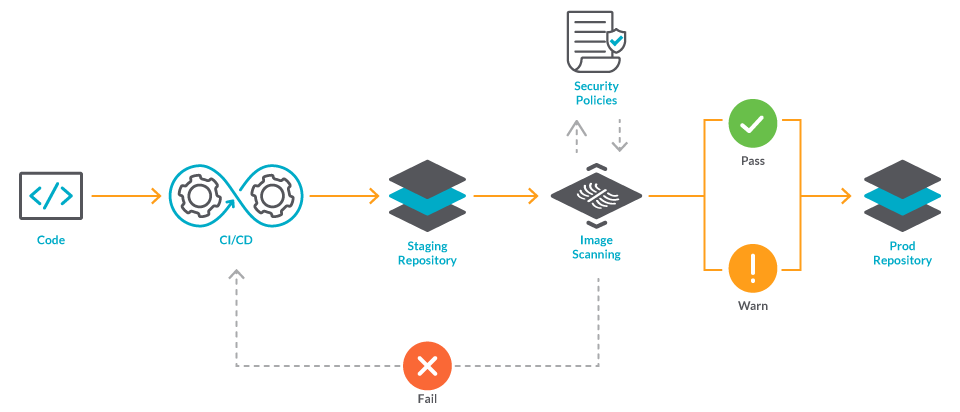
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

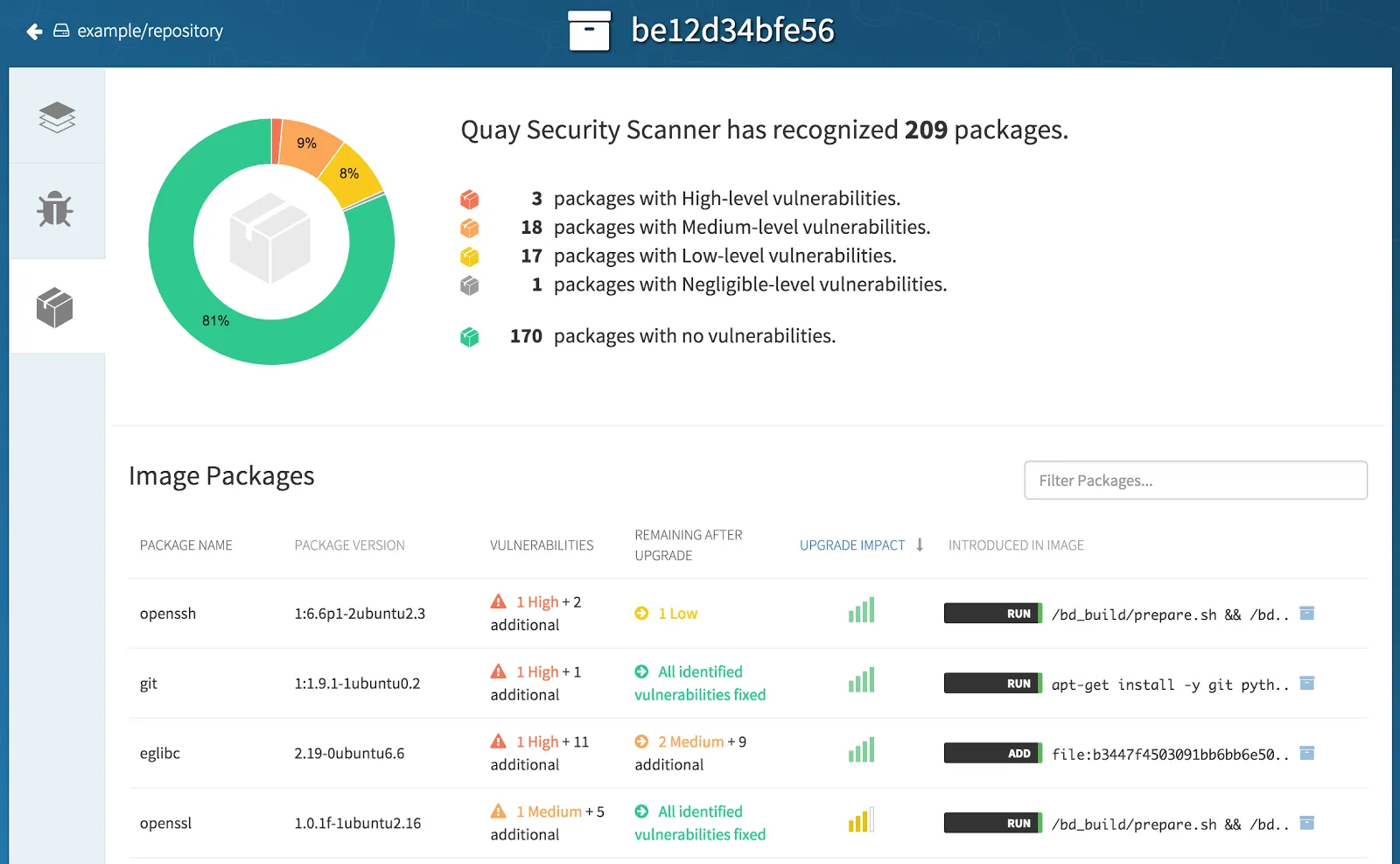
Guard against security vulnerabilities in your software supply chain with Container Registry vulnerability scanning | Google Cloud Blog